Proxy Servers: Usage and Configuration Guide
Every time you access the Internet, you get a unique identifier assigned to you known as an IP address. Your IP address can reveal a fair bit of information about you, including your location. Some websites can use it to block you from accessing their content. If you’re surfing the web from home, using an IP address provided by your Internet Service Provider (ISP), it can even be tied back to your name.
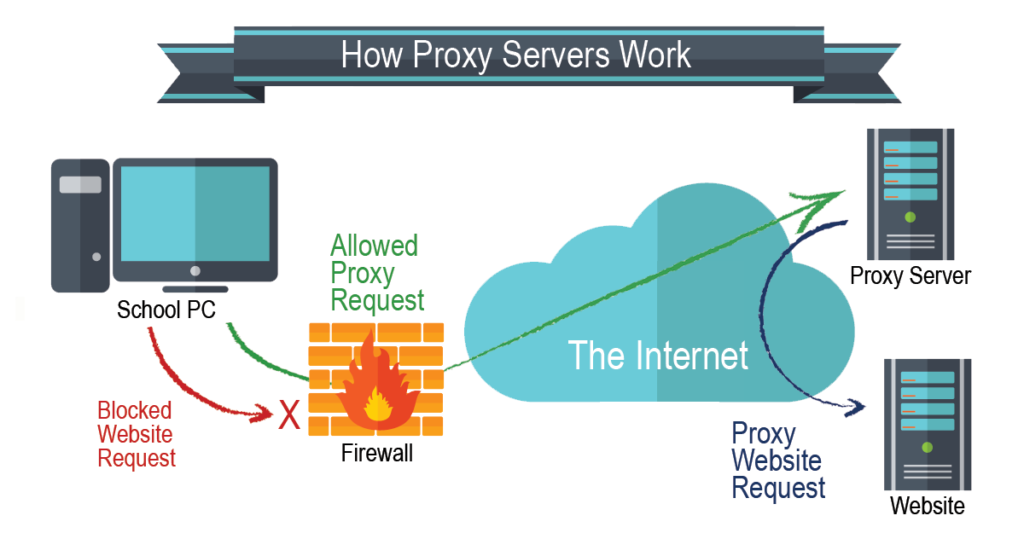
Hiding your IP address sounds like a good idea now, doesn’t it? One way you can hide an IP is with a proxy server. A proxy reroutes your request through a proxy server, so it does not go directly from your computer to your ISP to the website. That way, the website can’t see your IP address when you connect. To confirm what’s actually being exposed through a proxy (and whether it’s leaking your real IP), a proxy checker is a quick way to verify the connection.
A proxy server can be a useful tool for online privacy, but it can also have some downsides. This guide covers all the different types of proxies that are commonly used, as well as how to set one up on different web browsers.
Types of proxy servers
Even though all proxies help you access websites you might not otherwise get to, not all proxies behave the same way. Proxies come in several types, with slight variations in their functions.
Forward proxy
Forward proxies are the most common type of proxy server. The work by taking a request and passing it through from an isolated, internal network to the Internet through a firewall. An example is a company that uses a forward proxy server to route and filter employee traffic to the Internet.
Data center proxy
A data center proxy is an IP address that belongs to a data center like Digital Ocean or Amazon Web Services. These IP addresses are not affiliated with an ISP but with a data center. They use remote servers you can connect to when you want to hide your IP address. Data center proxies are more prone to blocking and blacklisting, however, and are more easily detected as proxies since they’re not issued by ISPs.
Residential proxy
Residential proxies are very similar to data center proxies, except that residential proxies use IP addresses that have been issued by ISPs. They’re connected to devices set up at specific locations so if someone tries to identify who is using the IP, it leads back to that location. These devices are part of a network set up by the ISP. Residential proxies provide a bit more security than data center proxies, but they’re slower.
Public proxy
A public proxy is what it sounds like: a proxy that is accessible by anyone on the Internet. It’s also known as an open proxy. For the most part, proxy servers work by only allowing users within a certain network or group to store and forward Internet services. Public proxies, therefore, are a bit of an exception. Since anyone can use them, anyone can find them, so they’re not great at keeping you completely anonymous online.
Shared proxy
Shared proxies are IP addresses used by multiple users at the same time. They’re the opposite of dedicated proxies, which are assigned to only one user at a time. The upside of shared proxies is that they’re cheaper than private proxy servers. But you can easily see how a shared proxy server — and a shared IP address — can be problematic. Performance, speed, and reliability are all low, plus all the activity of the other users can be traced back to you, since you all have the same IP address.
SSL proxy
Any proxy server that uses the Secure Socket Layer (SSL) protocol is an SSL proxy. They’re also referred to as HTTPS proxies (HTTPS meaning Hypertext Transfer Protocol). SSL and HTTPS protocols are basically methods websites use to secure the data that they process. HTTPS uses SSL to encrypt data as it passes from one endpoint to another. Since SSL proxies rely on encryption, they tend to be safer and more anonymous than proxies that don’t use SSL.
Rotating proxy
A rotating proxy does not assign you one IP address, but rather a pool of IP addresses. The IP address you use could change every few minutes or with every new request you make. Rotating proxies are super fast, making them useful for things like web scraping and data mining, where you need to make thousands of connection requests at the same time. Both data center and rotating proxies can be used as rotating proxies.

Reverse proxy
A reverse proxy does the opposite of a forward proxy. Rather than sitting in front of the clients like a forward proxy does, a reverse proxy sits in front of one or more web servers to intercept requests from clients. Forward proxies keep servers from interacting directly with clients; reverse proxies keep clients from interacting directly with servers.
Transparent proxy
Transparent proxies communicate to websites that they are proxy servers and will still pass along your IP address. So what’s the point? Transparent proxies can also be used by companies who want their employees to use a proxy without employees knowing about it. They’re easier to use because it feels just like connecting with your home Internet, but they’re also more susceptible to threats.
Distorting proxy
A distorting proxy doesn’t simply hide your IP, it will actually provide a false IP address to the website you’re trying to access. The server gives the impression that you’re connecting from another location, hiding the geolocation from the website. A distorting proxy is the proxy you want to use when you’re trying to get around geo-blocked content.
High anonymity proxy
A high anonymity proxy offers the highest level of privacy and security you can probably get with a proxy server. Not only does the server you connect to not receive any information about your IP address, but it also can’t even tell that you are connected using a proxy.
Different browser proxy
If you want to take advantage of the privacy and security that proxy servers can provide, you have to know how to set up a proxy server on your web browser. Generally, you’ll have to navigate to the settings or preferences of your browser and you’ll need to know the proxy server address. After you have that, it’s pretty straightforward.
Chrome browser proxy
Chrome uses the same proxy settings as the OS it’s running on. If you’re running Windows 10, here’s how to set up a Chrome browser proxy:
- Open a Chrome browser on your device.
- Select the three dots in the top right corner.
- Select Settings.
- Select Advanced from the column on the left side, then select the System tab.
- Click Open your computer’s proxy settings.
- The Windows 10 proxy settings should come up. Scroll down to Manual proxy setup and toggle the switch On for Use a proxy server. Ensure the switch for Automatically detect settings is toggled On as well.
- If you already have a proxy server available, Windows will provide the name and prompt you to follow the instructions.
- When Windows finds a proxy auto-config (PAC) file, you can get the setup script. Toggle the Use setup script button On, then enter the Script address.
- Click Save and return to Chrome. Your proxy should be set up now.
Firefox browser proxy
If you don’t want to use a proxy server with Windows 10, then you can browse the web with Mozilla Firefox instead. Here’s how to set up a Firefox browser proxy:
- Click on the Menu button (the three horizontal lines) in the top right corner.
- Click Settings.
- Scroll down to Network Settings and then click the Settings… button.
- You will see a pop-up named Connection Settings.
- Firefox uses Windows 10’s proxy settings by default, so you should see the Use system proxy settings option selected. You can change this, however, and configure a separate proxy server for Firefox.
- You can either select Manual proxy configuration and enter the proxy details or select Automatic proxy configuration URL and enter the address from your PAC file.
- You can select certain addresses you do not wish to use the proxy for by entering them, separated by a comma (,) in the No proxy for text box. This is optional.
- Once you are done, click OK. Your proxy should be set up now.
Advantages of using a proxy server
Why use a proxy server? There are several benefits, including:
- Privacy: If you want to look at something online but would prefer that it can’t be traced back to your IP address and location, you can use a proxy. You can also use a proxy if you want to post comments on a forum online without having it traced back to you.
- Security: Hackers have a harder time accessing your IP address when you use a proxy, so you’re protecting your computer or network from being infiltrated.
- Geo-blocked content: When you set up a proxy server, you can designate a specific location so that you can access content or websites that are locked to that region or country.
- Content control: If you’re a network administrator for a company or school, you can use a proxy to block access to certain websites that may be considered inappropriate or distracting from productivity.
- Speed: Proxy servers cache information about visited websites for retrieval later, so they don’t slow down your web browsing.
Disadvantages of using a proxy server
Proxy servers have some downsides, which you should be aware of before you use one:
- Data tracking: Caching information can help speed web browsing up but it can also make it easier for someone within the network to download all the stored data and access usernames, passwords, and other sensitive info. If you use a proxy server, make sure you find one that offers protection to prevent this kind of tracking.
- Weak encryption: Most proxy servers use standard SSL certification as an encryption standard, which is vulnerable to an attack known as SSL stripping. For a more robust encryption option, you should use a VPN instead.
- Technical know-how: Setting up a proxy server properly takes some settings configuration that usually only a network administrator can do.
- Cost: Setting up and maintaining a proxy server can be expensive if you’re using it for your company.
You should also keep in mind that your employer, your ISP and other networks might object to your using a proxy. Just because you can do it, doesn’t mean you should. And in some cases, websites will blacklist IP addresses they suspect or know are from a proxy.

What is an IP address locator?
An IP address locator provides you with the location, ISP, hostname, type, proxy, or blacklist status of an IP address. You can use an IP locator tool to find the geographic location associated with an IP address, although you most likely won’t be able to find a specific address.
An IP address lookup tool can also be used to determine if there is a proxy server behind your computer. Sometimes, proxies can be installed on someone’s computer without their knowledge, for nefarious purposes. Checking to see if there is an open proxy with your IP address could help you stay safe online.
To look up info about your IP address or another one, use our IP lookup tool.
What is an IP grabber?
An IP grabber is a tool that lets you spy on IP addresses across the Internet. They typically work by having the user click on a link, which directs to a website with the primary purpose of logging the user’s IP address. While an IP address locator can be used simply to gather information, an IP grabber is slightly less innocent. They can be used to extract an IP address for targeted advertising or finding a user’s location.
If you mistakenly click on an IP grabber link, it’s possible your device is now being tracked. The tracker may have access to personal information on your device. However, since your IP address changes, especially on a mobile device, it would be difficult for someone to find your exact location this way. In the same way these tools can be used to track IP addresses, they can also be used to track proxy servers.
Stay safe online
A proxy server can be a good choice if you’re trying to maintain your privacy online. They typically have more practical applications for companies or organizations than individuals, however. As an individual web user who wants to keep their IP hidden or change the location of their IP, a VPN usually works more effectively.
Related Articles
Related Articles
- All
- Easy Prey Podcast
- General Tech Topics, News & Emerging Trends
- Home Computing to Boost Online Performance & Security
- IP Addresses
- Networking Basics: Learn How Networks Work
- Online Privacy Topics to Stay Safe in a Risky World
- Online Safety
- Uncategorized
This Story of Elder Financial Abuse Reveals Warning Signs that Get Overlooked
Not all elder financial abuse stories start with a scam, or even an obvious problem. A friendly…
[Read More]Social Media Hacking Isn’t Random, It’s Data-Driven
You don’t have to click a malicious link to become a target. Sometimes, all it takes is…
[Read More]Scams Targeting Seniors Aren’t Going Away Soon.
So, what makes scammers an appealing target group for cyber criminals? Here’s what the consensus on that...
[Read More]What Art Fraud can Teach Us About Art, Fraud, and Buying Smart
In movies and on TV, the world of art fraud, forgeries, and theft is glamorous and exciting….
[Read More]Call the Local News for Fraud Help. Scam Victims Turn to an Alternative Resource for Results.
It’s frustrating for victims of scams and fraud who have taken what they believe are the right...
[Read More]Identity Theft Resource Center: Support, Education, and More
There are plenty of resources available to consumers to report crimes, scams, and identity theft. However, not...
[Read More]