Cryptocurrency Mining Malware: A Growing Threat

What is cryptocurrency exactly?
Cryptocurrency can best be described as a digital form of money. The “crypto” in the name comes from the cryptography, or coding, that’s part of the process. This includes standard computer coding as well as complex mathematical algorithms or “codes.”
Why cryptocurrency?
What’s desirable about cryptocurrency is that it’s decentralized. This means that the blockchain exists all over the world on the computers of the various miners and users. Anyone with access to the blockchain might potentially see the public key to your wallet. But the cryptography is so in-depth that they cannot easily guess or find your private key.
The original appeal for cryptocurrency is that it is completely anonymous. It was used as the currency of the dark web. This is partly because a decentralized currency managed exclusively by numbers is completely anonymous.
Another appeal of cryptocurrency is that it’s self-governed. After all, while banks are managing our money, if they’re also working with, and sometimes managing, your credit cards then there are conflicts of interest. If a bank knows your debt and income they may limit your ability to make more money.
Cryptocurrencies are open source but still manage to remain secure. That’s where those codes come in. These complex algorithms are run by miners that add transactions to the ledger of all crypto transactions, or blockchain. The blockchain is public. Wait, what?
How can something be open source and private at the same time?
Your cryptocurrency is stored in a crypto wallet. These wallets rely on 2 codes. There’s your public key and your private key. Think of it kind of like your account number and your routing number for your bank account. Imagine if your routing number was public, so anyone can see it and potentially send you money. But transactions can only take place, i.e. you take money out of your wallet, with your private key. The “coding” protects this code at all costs.
How does it work?
You don’t literally store your cryptocurrency in this wallet. Cryptocurrency wallets are used to keep the public and private keys of your cryptocurrency in one place in the same way your wallet gives you a place to keep your cash and credit cards.
If you’re new to crypto, you need a public key in order to be able to receive money. You need a private key to be able to make transactions with and use your cryptocurrency. All of your cryptocurrency lives on the blockchain, the digital ledger of all transactions. These keys help manage your “ownership” of the crypto in question.
So imagine we didn’t mine for gold. Instead, we logged every gold deposit in the world. Let’s say we assigned a number to them. You could own a deposit of gold in Africa. It increases in value as gold prices inflate. And let’s say you want to sell that deposit for cash to someone in Korea. Now they own that gold deposit. The gold has not moved at all but the ownership has changed hands.
Similarly, if you had bitcoin, the bitcoin never “leaves” the blockchain–its ownership is just being exchanged.
A Bit About Keys
Now, how do these keys work? On the simplest level, your public key is like your routing number and your private key is like your account number and signature.
Anyone can send you crypto using your public key. You can list it publicly like your Venmo or Cash app. Your private key, however, is what you use to verify transactions and do anything with the cryptocurrency. So you’ll want to keep that more private than your social security number. Anyone who has your private key can–if they know how–clean out your wallet.
The crypto in cryptocurrency is named for the cryptography and encryption that makes it possible for the entire blockchain to be public but for your currency to remain secure. 256-bit encryption is used to derive a private key from a public key.
While secure, that can be cumbersome for many. One evolution to cryptocurrency is new wallets will provide you with a mnemonic seed. This is a string of random words that correspond to your private key. It’s kind of like in Captain America: Civil War where a few random phrases turned Bucky Barnes into the Winter Soldier. But with these random phrases, you get access to some Bitcoin or Ethereum, not a super-soldier.
Different types of cryptocurrency wallets
Cryptocurrency wallets vary in their use, potential protection, and how easy they make it to use your cryptocurrency.
Let’s break it down:
What are the types of cryptocurrency wallets? There are three main types of wallets: paper wallets, software wallets, and hardware wallets. Additionally, a wallet can either be “hot” or “cold,” with hot referring to being on the Internet and cold meaning not actively on the Internet.
- Paper wallets are printouts of your private and public keys. This can also be manually written down versions of your private and public keys or the mnemonic codes for your wallet. Paper wallets also have QR codes that help you “sign” or validate your transactions.
- Software wallets are apps, web pages, or desktop applications that store your private and public keys. They also facilitate signing your transactions.
- Hardware wallets are external devices that help you keep your private and public keys off of your computer. This allows you to better protect the privacy of your keys, which is incredibly important, considering crypto prices can be so high that if you lose your private key or get hacked you could lose tens, if not hundreds of thousands of dollars.
For more on these wallet types click here.
A Bit About Websites and Apps
There are many websites and apps that facilitate crypto transactions like Coinbase or Robin Hood. Now, these can vary so you’ll want to know if your wallet is actually on the blockchain or not.
Oftentimes, these companies will not facilitate wallets so much as act as a middle man. Kind of like a bank. You buy and trade and they facilitate those transactions or allocate the crypto they manage to you. But they manage the transactions on the blockchain.
These are helpful services and a great way to get started. But it’s important to know where your wallet is and how your crypto is being managed.
Your smartphone could be hi-jacked by cryptocurrency-seeking cybercrooks.
Since Bitcoin’s high-profile year, the increasing popularity and real-world significance of cryptocurrencies has drawn the attention of cybercriminals and dramatically changed the threat landscape.
Drive-by mining is an automated, silent and platform-agnostic technique that forces visitors to a website to mine for cryptocurrency.
Malware-based miners are providing online criminals new revenue sources through forced crypto-mining on mobile phones and tablets. While far less powerful than a PC, there are billions of smartphones that can easily fall prey to illicit mining via “Trojanized” apps, redirects and pop-unders.
In 2017, Kapersky Lab researchers identified Loapi, a Trojan malware with several (and possibly endless) malicious features owing to its modular architecture, which includes adware module, SMS module, web crawler module, proxy module and notably, Monero miner module. Monero is a newer type of digital currency that’s less resource-intensive than Bitcoin and other cryptocurrencies. The mining module generates new coins by leaching the electricity and hardware of the infected phone. This type of attack is a prime example of a malware crypto scam, where unsuspecting users unknowingly contribute their device’s resources to benefit cybercriminals. Ironically, the malware creates such heavy workload on the infected device that it heats it up causing serious and permanent damage.
In recent months, a piece of Android malware was discovered carrying a secret and aggressive cryptocurrency miner that can physically damage an infected phone.
Malwarebytes first discovered the malware while the team was testing a malvertising chain on Windows and Chrome that would lead to tech support scams. When they tested the same chain on Android, they were “redirected via a series of hops to that crypto-mining page.”
The page features a warning message and a CAPTCHA code that users need to enter, otherwise, the website will proceed to mine Monero cryptocurrency (XMR) at full speed. Malwarebytes found several identical domains, all of which use the same CAPTCHA code, registered as early as November 2017 — the latest five domains however, were more recent. It’s estimated that the five domains receive around 800,000 visits per day, with visitors spending an average of four minutes on the site. The team puts the ballpark revenue at a few thousand dollars a month but given the volatility of cryptocurrencies, the profit could exponentially grow overnight.
This phenomenon isn’t limited to Android devices, no matter how fanatic Apple defenders are about their phone’s security features. Security firm SentinelOne revealed that a third piece of Mac malware (following OSX.Mami and OSX.CrossRAT) was being spread via hack of the MacUpdate site. The Mac Trojan, OSX.Creative Update, also harnesses CPU power to surreptitiously mine Monero.
Despite the above-mentioned hack of a trusted site, sticking to official websites to download applications still applies as a rule of thumb. Keeping your software up-to-date and using appropriate antivirus software, same way you would safeguard your PC, would greatly reduce the risks of cryptocurrency mining operation attacks on your mobile device.
Related Articles
Related Articles
- All
- Easy Prey Podcast
- General Tech Topics, News & Emerging Trends
- Home Computing to Boost Online Performance & Security
- IP Addresses
- Networking Basics: Learn How Networks Work
- Online Privacy Topics to Stay Safe in a Risky World
- Online Safety
- Uncategorized
What Is a Filter Bubble? How Algorithms Shape What You See Online
When you and your friend in another city search for the exact same thing on Google, you…
[Read More]AI Is Changing Privacy Laws–Here’s What You Need to Know
AI is everywhere. Even if you’re not logging into ChatGPT every day, everything you do on the…
[Read More]Browser Security Settings Make a Difference to Online Safety
If you’re getting online, you’re using a browser. Whether you’re a Firefox fan, a Chrome devotee, or…
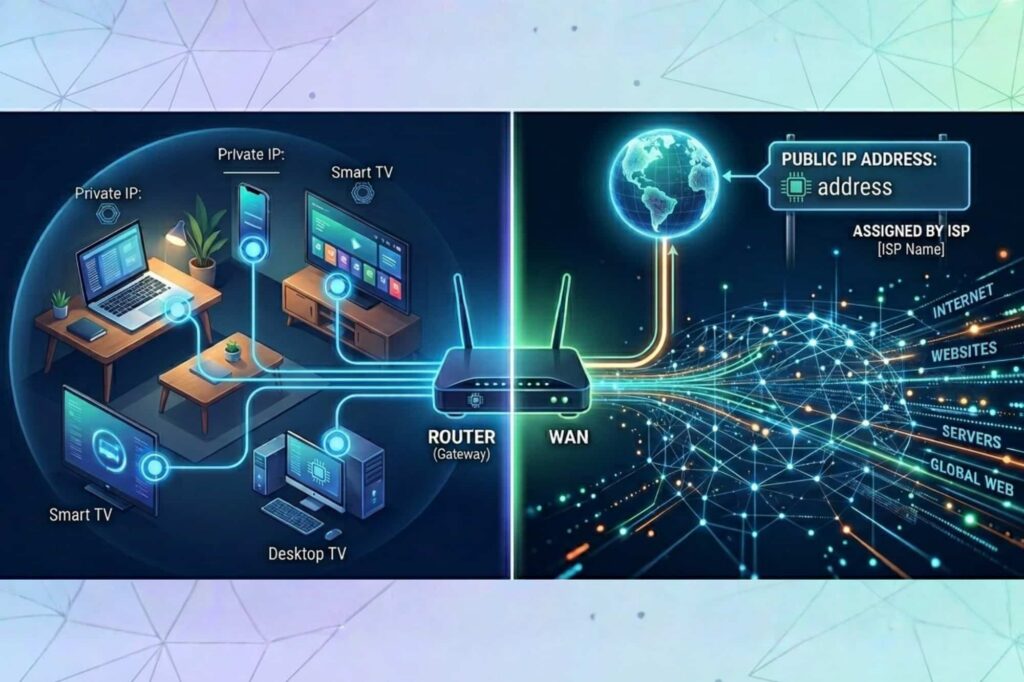
[Read More]Public IP vs. Private IP Address: What’s the Difference and Why It Matters
Have you ever looked up your IP address on a tool like WhatIsMyIPAddress.com’s tool and noticed what…
[Read More]What Is an IP Address and What Information Does an IP Address Reveal?
Every time you go online, you leave a trail, and your IP address is one of the…
[Read More]Investment Fraud: When Investing Losses Aren’t Just from Risk
If you invest money anywhere, you hopefully know that investing comes with inherent risk. But not every…
[Read More]